Cloud Quickstart
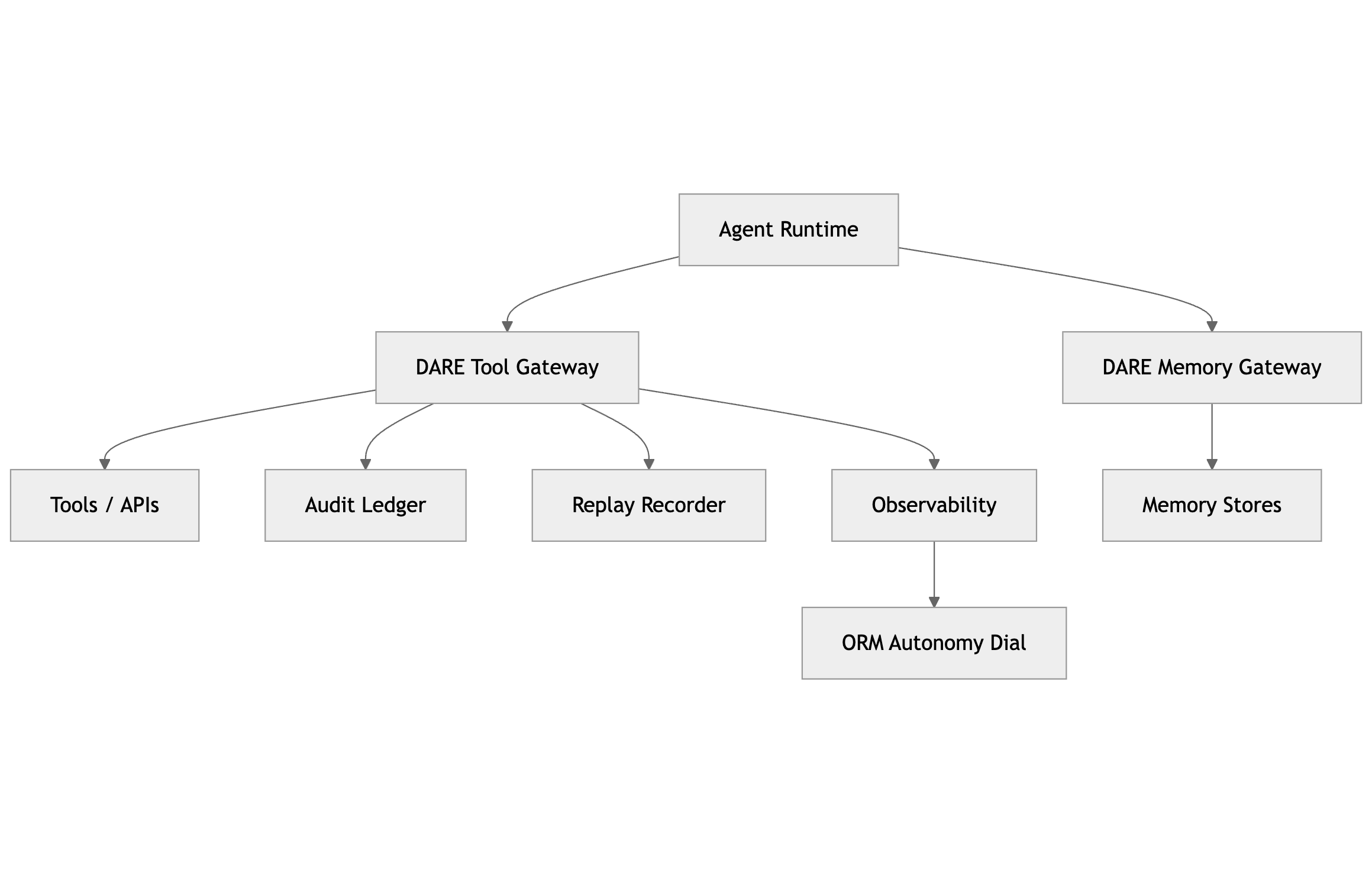
Minimal reference deployment patterns for a bounded GATE tier. This page shows what to deploy, where it sits, and how to preserve the no-bypass-path invariant.
- Tool Gateway: authenticate, policy-evaluate, budget, obligate (HITL/verify/redact), emit evidence.
- Memory Gateway: retrieval/write ACLs, provenance checks, TTL, poisoning quarantine, emit evidence.
- No bypass path: runtimes cannot reach tools/memory except through enforcement.
- Audit ledger: append-only, tamper-evident commits (hash-chained).
- Replay recorder: snapshots + pinned bundles (policy/tool schema/prompt bundle hashes).
- Observability: OpenTelemetry traces with run_id/trace_id correlation.
- Workload identity per agent instance (short-lived).
- Attestation where available (image digest/config/toolset claims).
- Service-to-service auth between runtime ↔ enforcement ↔ evidence.
- Policy-as-code (OPA/Rego or equivalent) used by enforcement points.
- Budgets/quotas enforced at the enforcement boundary (tokens, tool calls, cost).
- Obligations enforced (HITL, verify destination, redact fields).
- Network: runtimes cannot route to tools/APIs or memory stores directly (private endpoints + egress deny by default).
- IAM: runtime identity has no direct permissions to tool backends / data stores; only enforcement identities do.
- SDK: agent SDKs must call your gateway client; direct connectors should be removed or disabled.
- Secrets: no long-lived API keys inside agents; use short-lived tokens minted for each governed request.
Logical view of the governed boundary. Your concrete cloud mapping should preserve the same constraint: runtimes do not directly access tools or memory, and every governed operation produces evidence.
Before you grant high-impact permissions, prove enforcement and evidence end-to-end with must-pass checks. Start with a single low-risk tool and a single memory store, then expand.
- No tool execution without a policy decision record linked to the request hash.
- No direct runtime path to tools/memory (network + IAM + SDK constraints).
- Every privileged action is attributable (agent_instance_id + run_id).
- Replay reproduces the run at the governed boundary using recorded snapshots + pinned bundles.
- Start “observe-only” for policies, then enforce for high-risk tools first.
- Default-deny new tools until schemas and policies are registered.
- Introduce HITL obligations for irreversible write and financial tools.
- Use orchestration backpressure for macro health; keep gateway budgets for micro limits.
AWS Quickstart
Minimal mapping of GATE components to AWS primitives. Choose managed services where possible, but preserve the enforcement boundary.
- Runtime: EKS/ECS/Fargate/Lambda (your agent host)
- Tool Gateway: ECS/EKS service (or Lambda + API Gateway for simple cases)
- Memory Gateway: ECS/EKS service (placed in front of vector/state stores)
- Policy: OPA sidecar/embedded; policy bundles in S3 + signed releases
- Identity: IAM roles for service accounts (EKS IRSA) + OIDC; short-lived STS
- Evidence: S3 Object Lock (WORM) for ledger/replay artifacts + Athena/OpenSearch for queries
- Observability: ADOT (OpenTelemetry) → CloudWatch/X-Ray/OpenSearch
- Secrets: Secrets Manager + KMS
- Put tools/memory behind private endpoints (PrivateLink where applicable).
- Runtime security groups/NACLs: deny egress to tool/memory networks except gateway.
- IAM: runtime roles have no permissions to tool backends or data stores; only gateway roles do.
- API keys/tokens are minted and scoped by the gateway; no static keys in agent containers.
Recommended “bounded” defaults
- Budgets at gateway: max tool calls per run, max cost per run, per-tool rate limits.
- Obligations: verification required for destination changes; HITL for irreversible writes and finance.
- Evidence: ledger commit for every privileged operation; replay snapshots for every tool response.
Azure Quickstart
Minimal mapping of GATE components to Azure primitives. The boundary remains the same: no direct runtime access to tools or memory.
- Runtime: AKS / Container Apps / Functions
- Tool Gateway: Container Apps / AKS service (optionally fronted by APIM)
- Memory Gateway: Container Apps / AKS service (fronting vector/state stores)
- Policy: OPA sidecar/embedded; policy artifacts in Blob Storage + signed releases
- Identity: Managed Identity + workload identity federation (AKS)
- Evidence: immutable storage via Blob immutability policies; query via Log Analytics / Data Explorer
- Observability: OpenTelemetry → Application Insights / Log Analytics
- Secrets: Key Vault
- Use Private Endpoints for tools and data services where possible.
- Lock down egress from runtime subnets; only gateway can reach tool/memory endpoints.
- RBAC: runtime Managed Identity has no direct access to tool/data resources.
- Evidence stores enforce retention/immutability; avoid plaintext PII in immutable logs.
Recommended “bounded” defaults
- APIM (optional) for front-door rate limits; still enforce decisions in the gateway itself.
- Key Vault-backed envelope encryption for sensitive evidence payload pointers.
- Replay recorder stores tool snapshots in immutable storage and pins policy/schema hashes per run.
GCP Quickstart
Minimal mapping of GATE components to GCP primitives. Aim for Cloud Run or GKE first, and keep the boundary hard.
- Runtime: Cloud Run / GKE
- Tool Gateway: Cloud Run service / GKE service (optionally behind API Gateway)
- Memory Gateway: Cloud Run service / GKE service (fronting vector/state stores)
- Policy: OPA sidecar/embedded; policy bundles in GCS + signed releases
- Identity: Workload Identity Federation (GKE) / service accounts (Cloud Run) with short-lived tokens
- Evidence: GCS retention + Bucket Lock for WORM-like retention; queries via BigQuery (exported logs/events)
- Observability: OpenTelemetry → Cloud Logging / Cloud Trace
- Secrets: Secret Manager + Cloud KMS
- Use Private Service Connect / VPC connectors for private access patterns.
- Restrict egress from runtime (VPC-SC / firewall rules) so only gateways can reach tool/memory services.
- IAM: runtime service account has no direct permissions to tool APIs/data stores.
- Evidence: export structured events to BigQuery with retention rules; keep immutable artifacts in locked buckets.
Recommended “bounded” defaults
- Gateway budgets + per-tool allowlists; treat external HTTP tools as high-risk by default.
- Memory gateway enforces retrieval-time ACLs and TTL; quarantine on provenance failure.
- Replay harness stores tool snapshots and mocks identity/policy verification for long-lived replays if keys rotate.
- Pick one tool (low-risk) and route it through the Tool Gateway with policy + evidence.
- Add memory behind the Memory Gateway (ACL + provenance + TTL) and record access evidence.
- Run conformance for bypass, decision-record linking, replay validity, and ledger integrity.
- Expand safely: add tool categories, obligations, then HITL for irreversible write/financial actions.